Three Common Pitfalls in Cloud Computing and How to Manage Them Effectively
Welcome to our series on security governance, focusing on the crucial aspects of governance, risk management, and compliance within organizations. In this edition, we delve into three common pitfalls in cloud computing: cloud misconfiguration, inadequate third-party risk management, and the often-overlooked shadow IT. We will explore effective strategies to address and excel in managing these challenges, empowering you to enhance your cloud environment's security. Stay informed and ensure your organization's cloud infrastructure remains robust and secure.
Cloud misconfiguration
As innocuous as it seems, misconfiguration and insecure configurations contribute to a vast majority of successful attacks. As the states shows that more than 70% of the organizations using cloud infrastructure has at least 1 security misconfiguration whereas more than third of the cyber incidents are due to the misconfigurations.

According to exhaustive research conducted on thousands of web applications by the Open Web Application Security Project (OWASP), a whopping 90% of web applications were detected to have some form of misconfiguration. Some of the most notorious forms of misconfiguration include having built-in accounts and their default passwords enabled, unnecessary ports and features being enabled, missing security patches, and overly informative error messages.
So, what are the top countermeasures against misconfiguration?
The simple answer is “Start secure and Stay secure" throughout the lifecycle of the application or system. Starting secure translates to ensuring an adequate hardening process prior to going-live, and staying secure is about ensuring sound change management and configuration management practices are followed. However, starting secure and staying secure are easier said than done. In a typical environment, with a focus on agility, speed and with software development paradigms such as DevOps, there is often a tremendous pressure to go-live on time, as driven by business need.

It comes down to the security leadership and indeed the entire team to ensure that CI/CD does not result in CV - Continuous Vulnerability!
By adopting a compliance measurement framework, such as the CIS benchmarks continually, enterprises can detect and respond to insecure configurations with more agility.
Lack of third-party risk management
We have all heard about at least one major data breach caused by threat actors exploiting a vulnerability in a third party's systems. From SolarWinds to MOVEit to Okta, exploitation of vulnerabilities within the infrastructure of third parties has proven to be quite an attractive target for threat actors.
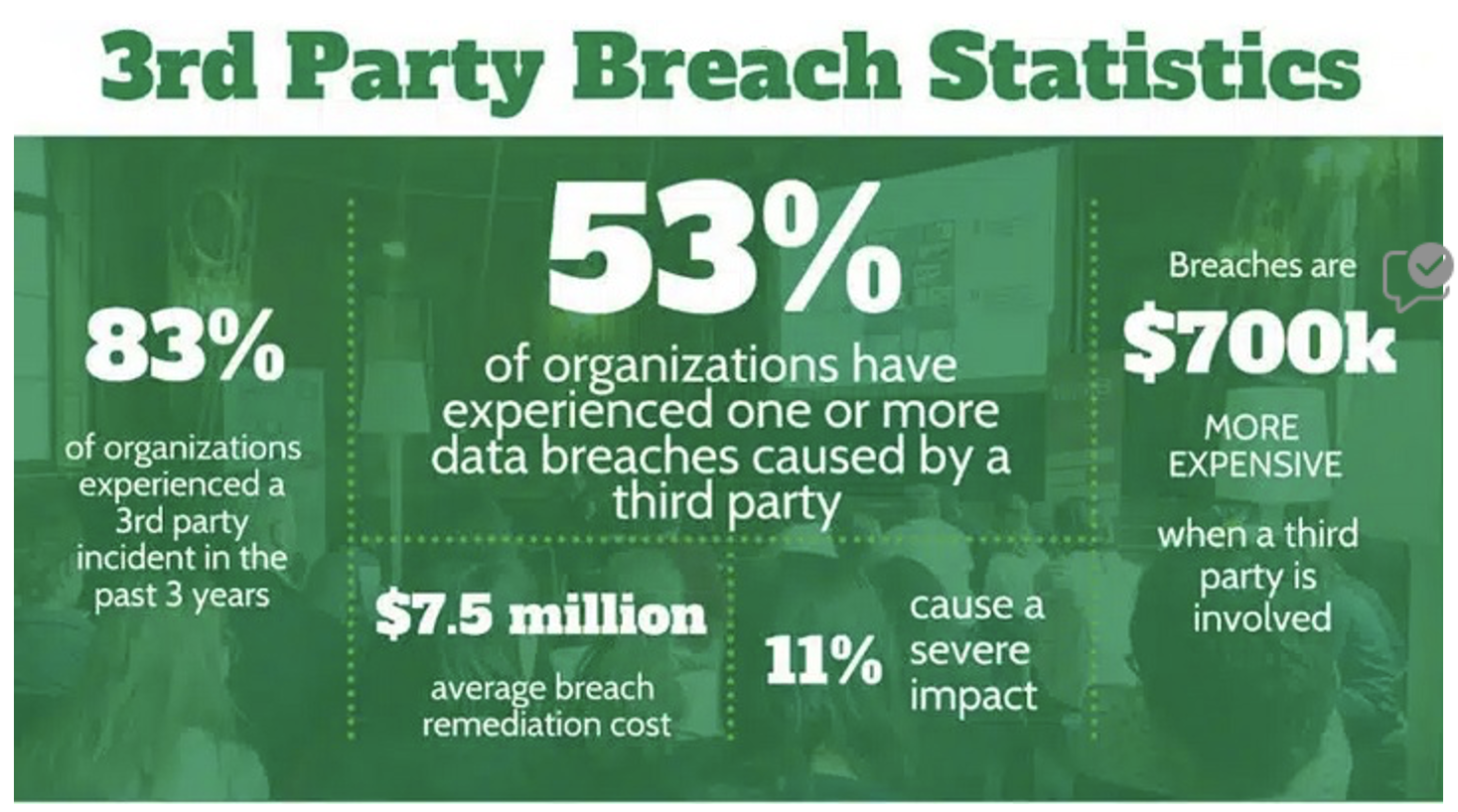
The sheer number of data breaches and successful attacks because of an insecure third party is so high that this could well be the elephant in the room for security.
Research of 235,000 organizations globally and 73,000 vendors by SecurityScorecard discovered that 98% of organizations have integrations with at least one third-party vendor who has been breached in the last 2 years. That is an astonishing number.
The challenges are often complicated by the number of your and your third parties’ dependencies ("fourth parties"). Third party risk management is essentially an expansion of supply chain risk management in this context.
Here are several effective practices to ensure that you are on top of this rapidly emerging risk.
- Integrate Third Party Risk Management process into your organization's risk management processes.
- Keep an accurate inventory of your third parties (Customers, suppliers, contractors, etc.), and your exposure to each.
- Do your due diligence before you decide to associate with any third party.
- Ensure that contracts include specific clauses on cyber risk, such as the right to audit, assurance by the third party of sound security practices, as well as immunity from downstream liabilities. This last one could well be the difference between a 5M $ fine and business-as-usual, should things go wrong with your third party.
- Monitor changes to your third-party risk environment, just as you would monitor your own risk environment.
Shadow IT and the resulting poor visibility
Shadow IT involves the use of unapproved software, hardware, systems, or services within an organization. This risk, while present in traditional IT settings, becomes significantly heightened in cloud environments, often exacerbated by phenomena such as SaaS sprawl. The primary driver behind Shadow IT is business users' desire to augment functionality and capabilities independently.
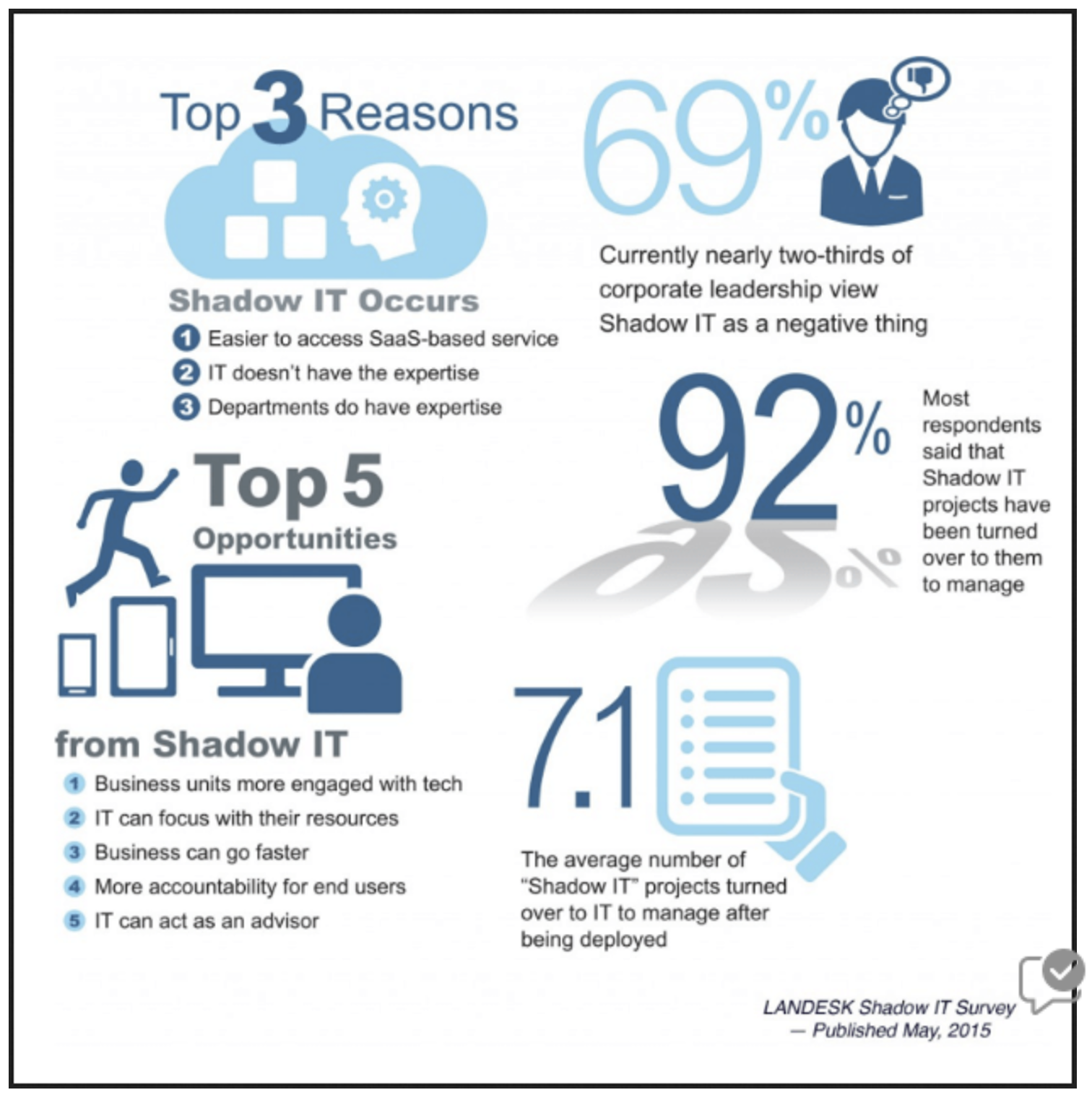
In many enterprises, users possess the ability to set up cloud resources without formal authorization, elevating the risk levels. A BetterCloud survey revealed a startling statistic: 65% of SaaS tools in enterprises are used without official sanction, often adopted covertly, bypassing the IT department.
This presents the classical security dilemma: How do you secure 235,000 tools that your teams is using you cannot see?
Below are some practices to reduce and better manage the risk of shadow-IT.
- Implement a policy within your organization that outlines rules for provisioning and using cloud resources. This policy could be part of your Acceptable Use Policy (AUP) or a dedicated Shadow IT policy. Its goal is to establish clear guidelines for employees and contractors regarding cloud resource usage.
- Embrace a Cloud Security Posture Management (CSPM) strategy, ensuring ongoing discovery and oversight across multiple cloud platforms. While specialized CSPM and Cloud Access Security Broker (CASB) tools are available, similar results can be achieved by engineering and automating your current tools.
- Engage with end users to understand their business needs and any limitations they might face with existing applications. This approach addresses the underlying causes of shadow IT and helps mitigate its risks.

Additionally, incorporating the topic of shadow IT into security awareness training sessions is another effective method to prevent risks.
Although we've highlighted three prevalent challenges, the spectrum of risks in cloud computing is extensive.
PKF Antares assists organizations in significantly enhancing their cybersecurity maturity. Our services, encompassing maturity assessments and cyber resilience strategies, are designed to yield concrete improvements. To discuss how we can support your cybersecurity needs, click here to connect with one of our experts.